11.30.11
Posted in Culture of Lickspittle, Cyberterrorism at 1:04 pm by George Smith
A long time ago I had a book by John Dvorak. It was on shareware telecomms programs and was about 800 pages. If if I hit you in the face with it, it would have broken your jaw.
Dvorak was a legend in computer trade publishing and, in my mind, not in a good way. He was one of a common breed, someone who turned out trade books eiither written by machine or a small number of office
flunkies.
Anyway, today Dvorak’s name rose to the top of the Google pile for a PC Mag piece he authored on the set-yer-HP-laser-printer-on-fire story.
Many have covered that news responsibly so I won’t get into the details here.
However, there’s one bit from Dvorak, worth pulling out, just to show things never change. He’s an empty machine who phones it in.
And here’s the proof, from a piece of comment on the HP printer flaw:
This reminded me of the other recent hack whereby a hacker got some code into a power plant or some such thing. The hacker began to turn the pumps on and off so fast that the mechanisms overheated and either stopped working or caught on fire.
If you’ve been reading here — or any other reasonable security publication — you know this story was reported as unfounded last week.
John C. Dvorak — today’s example of someone so spent, fat, lazy and full of himself he can’t do the most elementary checking. This made worse by copy editors at PC Mag too cowed to do their job and save the man from himself.
Dvorak’s brief Wikipedia entry makes little mention of his work as a producer of computer books as really big paperweights .
However, it is refreshingly negative:
He has also gained some notoriety for making predictions that have turned out to be spectacularly off-target …
Dvorak is a skilled BBQ and grilling enthusiast, noted collector of Bordeaux wines and has been a tasting judge at various international events. He started his career as a wine writer.
You can tell all that.
Permalink
11.25.11
Posted in Cyberterrorism at 12:05 pm by George Smith
Last weeks story on an alleged cyberattack on US infrastructure has been turned off like a drip from the faucet.
That story — mentioned in this post — went viral in the news media and involved an anecdotal report on a hack attack said to have burned out a water pump in Springfield, Illinois.
A Dept. of Homeland Security statement, widely distributed to various news agencies, reads:
“After detailed analysis, DHS and the FBI have found no evidence of a cyber intrusion into the SCADA system of the Curran-Gardner Public Water District in Springfield, Illinois …There is no evidence to support claims made in initial reports–which were based on raw, unconfirmed data and subsequently leaked to the media–that any credentials were stolen, or that the vendor was involved in any malicious activity that led to a pump failure at the water plant. In addition, DHS and FBI have concluded that there was no malicious traffic from Russia or any foreign entities, as previously reported. Analysis of the incident is ongoing and additional relevant information will be released as it becomes available.”
The original alarm raised by a security worker — here — and now expunged (oh, the humanity) generated a me-to-did-water-hack piece at the Register, a place I used to write for until they got weird and went entirely for the libertarian I-have-Asperberger’s demographic.
Which I won’t link to since it’s most probably rubbish, too.
Faucet electronic Pearl Harbor, it appears, has not yet arrived despite sincere efforts to make it seem so.
Permalink
11.18.11
Posted in Crazy Weapons, Cyberterrorism at 3:10 pm by George Smith
The story of the water pump in Illinois guarantees a viral eruption of stories exploring the post title.
Right now the evidence is small beer and still anecdotal.
Give it a couple days until eruption of all the potentials for attacks on the national infrastructure, stories with headings loosely based on “Have we just had an electronic Pearl Harbor?” and “Our new electronic Pearl Harbor!”
Permalink
11.17.11
Posted in Culture of Lickspittle, Cyberterrorism at 2:21 pm by George Smith
“U.S. national security endangered by China�s army of hackers,” reads the subhed in an opinion piece a couple days ago at the WaTimes.
From old man author William Triplett III:
In November 1997, Deputy Defense Secretary John Hamre testified before the Senate Subcommittee on Terrorism that �we�re facing the possibility of an electronic Pearl Harbor. � There is going to be an electronic attack on this country some time in the future.??? Two years later, he told a secret session of the House Armed Services Committee, �We are at war – right now. We are in cyberwar.??? Fast-forward more than a decade, to 2011. President Obama�s choice for secretary of defense, Leon Panetta, tells the Senate Armed Services Committee at his confirmation hearing that the United States faces a possible �electronic Pearl Harbor.??? Mr. Panetta had been the CIA director for the previous two years – so he would have known.
Two extreme, nearly identical warnings 12 years apart should have brought home the magnitude of the electronic threat facing the country.
From way back in November 1999, William Triplett III, pimping a book on the Red Chinese menace, in the pages of the Washington Times, taken from the old Crypt Newsletter archive on “electronic Pearl Harbor:”
The Washington Times is what Congressmen, particularly Republicans, read regularly before work. As such, material in it is influential in decision-making.
This particular piece continues the current Zeitgeist thread in which mainland China is painted as a threat.
“It is essential to have an all-conquering offensive technology and to develop software and technology for Net offensives so as to be able to launch attacks and countermeasures on the Net, including information-paralyzing software, information-blocking software, and information-deception software,” Gertz quoted a Chinese military publication as stating. He neglects to mention that US Department of Defense print similar tripe fairly regularly — and have done so for most of the decade.
Pentagon “anonymoids” show up on schedule: “A senior Pentagon official said he was notified about the article, which has raised concerns among defense officials who see China’s information warfare capabilities as a potential threat to U.S. civilian infrastructures . . .”
An “expert,” “William Triplett, co-author of a new book on the PLA,” said: “All of this offensive-warfare talk, when China is not threatened by anyone, shows that the dragon is at the point where it doesn’t have to hide its claws.”
Then the scary hypothetical scenario of catastrophe is produced.
According to Triplett, by way of the Washington Times, “China could launch a devastating computer-run sabotage operation by attacking U.S. oil refineries, many of which are grouped closely together in areas of Texas, New Jersey and California.”
“A [Chinese] computer attacker could penetrate the electronic ‘gate’ that controls refinery operations and cause fires or toxic chemical spills . . . “
China has what appears to be a vigorous offensive/defensive hacking operation for the purposes of intelligence gathering. So does the United States.
What makes the “electronic Pearl Harbor” meme different now — although still risible — is its use in justifying defense-spending for those parts of the plutocracy many of us find most detestable.
Wall Street, high finance and, as targets mentioned by the WaTimes opinion piece: “DuPont, Johnson & Johnson, General Electric, RSA, Epsilon, NASDAQ and at least a dozen other firms.”
“Alan Paller, a security expert at the SAND [sic] Institute, observed, ‘The depth of the penetration is more than anybody is admitting,” it reads.
Actually, it’s the SANS Institute. Although SAND as in “to sandbag” is accidentally danger close.
File under durable meme, used solely for enrichment of a section from the 1 percent.
Permalink
10.31.11
Posted in Cyberterrorism, Made in China at 4:10 pm by George Smith
Three years ago US Landsat satellites were diddled.
A piece at GovExec explains the events at length. And China gets most of the blame although I was unwilling to go quite that far:
China may have been flaunting its scientific capabilities by meddling with U.S. Earth observation satellites in past years, according to space and computer security experts.
Two unusual incidents involving signals targeting a U.S. Geological Survey satellite in 2007 and 2008 were referred to the Defense Department for investigation, USGS officials said Monday. NASA also experienced two “suspicious events” with a Terra observational satellite in 2008, officials at the space agency confirmed. An annual report from the U.S.-China Economic and Security Review Commission slated for release Nov. 16 is expected to characterize the events as successful interferences that may be linked to the Chinese government.
“I would say they were demonstrating the science and technology to be able to see what they could gain from it,” said Charles Vick, a senior analyst at GlobalSecurity.org who has been briefed on other government reports about China’s cyber skills. “To a degree one would think that [getting caught] was part of the mentality. It’s a warning. We could do this and a few other things.”
Since the event appears to have been trivial and is now three years old — AND is being publicized at a time when budget-cutting fever is in, I explained to the journalist one of the potential reasons were finding out about it.
Ammo for rationalizations on positive cyberwar/cyberdefense spending. Which readers know is always in vogue.
The journalist agreed this was one sound explanation and nicely addressed it near the end of the piece:
As hackers target U.S. computers with increasing intensity and frequency, the White House on Friday took the unusual step of asking Congress to pass stalled cybersecurity legislation. At first the Obama administration was the slow actor, taking a year to tell Congress which pending measures the president would enact. Now, with pressure to pass other bills, including a Dec. 23 deadline for deficit reduction legislation, the House and Senate are unlikely to agree on comprehensive reforms this year, experts say.
Obama cyber czar Howard Schmidt on Friday tried to light a fire, writing on the White House blog, “Unfortunately, time is not on our side. Since the White House delivered the administration’s proposal to Congress, a number of new security breaches have been reported. We need congressional leaders to move forward with a cross-committee and bipartisan approach.”
“The time is ripe to make proposal into law, and give the government and private sector the extra tools needed to fight those who would harm us,” Schmidt wrote on a White House blog.
Saideth me:
George Smith, a senior fellow at GlobalSecurity.org, said he would be surprised if the Chinese government was behind such sloppy execution, speculating that this may have been practice for a more aggressive attack.
“It would seem unusual to me that they would fiddle with satellites — which gets up the United States’ antennae — and then get caught with it,” he said. “That doesn’t rule out that this was a nation state doing a test run” …
As to why the government is making these sensitive events public now, Smith pointed to the federal government’s push for additional cyber defense funding.
Decent article covering all the bases and quoting from a variety of sources on different sides of the line. Read it here.
Permalink
10.19.11
Posted in Crazy Weapons, Cyberterrorism at 9:04 am by George Smith
Earlier in the week some clown at the Washington Post called the advent of the Stuxnet virus the “Hiroshima” of cyberspace.
Yesterday’s news of the Duqu virus generated some queries to your host. And if the world computer virus proliferation network works the way it always has, soon some windbag will have to talk about the cyberspace equivalent of a massive thermonuclear exchange.
However, to make this one short, I’ll describe one of the basics of computer virus proliferation.
Once out, there is no controlling what others might do to your creation. So, at this point it cannot be known with absolute certainty if Duqu’s creators were Stuxnet’s.
In any case, I’m sure the media will fill up with all kinds of spontaneously-generated theories on the subject.
The nut of my argument is this:
The history of malware generation and proliferation tells us that once a certain piece is in circulation others build upon it. In fact, there has always been a great enthusiasm for doing so.
Therefore, malicious s code eventually either gets distributed or becomes an open book to those in the malware art interested in adopting pieces of it for their own purposes.
It becomes game for others to analyze and use.
Stuxnet was widely distributed to many computer security experts. Many of them do contract work for government agencies, labor that would perhaps require a variety of security clearances and which would involve doing what would be seen by others to be black hat in nature. When that happened all bets were off.
So, to summarize, once a thing is in world circulation it is not protected or proprietary property. Such malicious code may contain hindrances to copying or reverse engineering but these can be overcome given enough effort. Add to this the fact that source code for malware has never been secure. It always becomes something coveted by many, often in direct proportion to its fame.
Therefore, it would not be surprising given the Byzantine and
secretive interlinked nature of this world, that Stuxnet code had leaked, even if only in bits and pieces.
Permalink
10.17.11
Posted in Culture of Lickspittle, Cyberterrorism at 7:21 am by George Smith
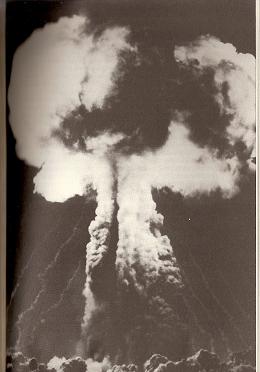
Stuxnet virus compared to Hiroshima atom bomb blast by some tool at the Washington Post.
Today, some run-of-the-mill stooge at the Washington Post, Dominic Basulto, furnishes us with perhaps the ten or thirty thousandth story on “electronic Pearl Harbor” in the last fifteen years.
Go ahead, try and count them. Quite a few are in Google. Your hair will go gray and fall out from the repetition.
It features all the cliches and over-the-top exaggerated claims one would expect in such a thing.
A sampling:
Rest assured, playing havoc with the U.S. power grid would cause more than traffic snarls on Main Street and random power outages � it would be the equivalent of a premeditated attack on U.S. soil. A single cyberattack would be, according to scenarios outlined in the Financial Times, equivalent to 50 hurricanes hitting at once, causing up to $700 billion in damage and crippling the country for weeks. What�s most concerning is that this cyberattack would not necessarily have to be carried out by a sovereign power � it could just as easily be carried out by terrorist cells in a place like Iran or Yemen.
So what would an [an electronic Pearl Harbor] strike on a nation�s infrastructure look like?
Stuxnet was the equivalent of launching a nuclear strike in the digital era. It was the �Hiroshima of Cyber War.”
Dead and injured from the Hiroshima blast = 135,000.
Dead and injured from “cyberwar” = 0.
“I like to think big thoughts that change companies,” reads the Post author’s tagline on Twitter.
Permalink
10.16.11
Posted in Cyberterrorism at 2:25 pm by George Smith
Yours truly from an interview on the drone virus non-story catalyzed by squealers to Wired last week (including a couple nifty quotes, one taken direct from 3-mail):
The U.S.�s fleet of unmanned aerial vehicles may not have been poisoned, after all …
Malware and spyware, Smith argues, have probably been found wherever the U.S. has networked computers involved in killing people.
Smith, who wrote one of the first books on computer viruses in 1994, speaks of Windows viruses in Yugoslavia and Serbia around that time; a virus that burrowed into two laptops on board the International Space Station in 2008 …
�Fighting viruses, by very definition, is reactive. It can never eliminate the problem entirely. There�s always a window.???
There’s more from motherboard.tv at the link.
Permalink
10.13.11
Posted in Cyberterrorism, Phlogiston at 2:21 pm by George Smith
The content/word cloud generator used to provide “related” links to posts made at Globalsecurity.Org always provides unintentionally great found humor.
When such software is used to crunch the words of your standard dullard it’s not worth a second look.
Now, munching through a DD word mass produces another thing entirely.
Here’s the one the software spat out after analyzing a syndicated copy of my post on the Predator drone virus story earlier today.
Ausgezeichnet!
Permalink
Posted in Cyberterrorism at 7:59 am by George Smith
Computer viruses/malware on US military networks are not remarkable. Ever since I wrote a book on computer viruses in 1994, so it has been.
Some of them rise to newsworthiness. Most don’t.
Because Wired pushed the news of a virus on a computer network administering Predator drone missions out of Creech AFB in Nevada, a fairly nothing story went … viral.
Every reporter who contacted me was working from a partial script that required they ask if this virus was a cyberattack from some other country.
And that’s because the US press has been amply fertilized with manure-filled stories and claims about how cyberwar and malware pose existential threats to this country. Consequently, because these stories are titillating and guarantee eyeballs on the net, everything that’s published in the area is viewed through the absurd lens of “Could it be cyberwar?”
The Creech drone virus, according to a report in a Las Vegas newspaper today, was a prosaic piece of random spyware aimed at stealing log-in information for on-line gaming. And it should not have risen to the level it did.
It’s most distinguishing feature, then, was that it was a virus made famous through exposure by loose-lippers and gossips at Creech — which operated Predators — to Wired.
That newspaper called upon your host. And as a GlobalSecurity.Org Senior Fellow I explained to its military reporter that computer viruses on military networks have never been rare.
Which is what I’ve told people ever since the news first broke.
In e-mail to reporter Keith Rogers, I wrote: “The military is exposed in the same way as everyone else on the world network.”
Mr. Rogers thanked me for my prompt and cogent public information service.
Note:This Las Vegas agency sues people on the web who quote from it as extortion for the extraction of cash money from those targeted. The story is easily Googled.
Previously.
Permalink
« Previous Page — « Previous entries « Previous Page · Next Page » Next entries » — Next Page »