03.25.14
Posted in Culture of Lickspittle, Cyberterrorism at 12:18 pm by George Smith
From Politifact…
Progress on a national cybersecurity framework, but trust shattered by Snowden revelations:
During his 2008 presidential campaign, Barack Obama promised to “ensure that his administration develops a Cyber Security Strategy that ensures that we have the ability to identify our attackers and a plan for how to respond that will be measured but effective.”
In the year since our last ruling, the attention devoted to cybersecurity has only increased, partly due to well-publicized breaches of customer data but especially from revelations about National Security Agency surveillance of electronic and telephone traffic.
On Feb. 12, 2013, Obama signed an executive order on “Improving Critical Infrastructure Cybersecurity,” which called for the implementation of a cybersecurity framework launched one year later …
The adoption of the framework is voluntary, but the Department of Homeland Security has established the Critical Infrastructure Cyber Community Voluntary Program, C-Cubed for short, to increase awareness and use of the framework …
So the administration has taken some concrete steps to develop a formal cybersecurity strategy. But the administration’s ability to pitch that strategy to private-sector companies and individuals has been hampered by the continuing stream of revelations based on leaked documents from former NSA contractor Edward Snowden. Whatever trust existed between the government and private companies has taken a serious blow in the post-Snowden era.
“On one hand, we had the Obama administration working for development of increased cybersecurity through its ‘framework’ initiative,” said George Smith, a senior fellow at GlobalSecurity.org. On the other hand, Smith said, the administration was “allowing the NSA to aggressively pursue initiatives that destroy the security and trust in global as well as domestic networks.”
So while Obama has made meaningful strides in creating a cybersecurity strategy, he faces stiffer-than-ever hurdles in implementing such a strategy, due to resistance in Congress as well as public skepticism.
The original — here.
Meta: There’s no skills or brainpower shortage in America. Check the paradox. I’m unemployed, skint, someone detested by corporate America, for even the lowest jobs in the new economy. But I’m the expert.
Permalink
02.14.14
Posted in Culture of Lickspittle, Cyberterrorism at 4:28 pm by George Smith

Someone had to pay for Edward Snowden and it damn well isn’t going to be Keith or Mike McConnell of Booz Allen:
The director of the N.S.A., Gen. Keith B. Alexander, is retiring next month after serving far longer than his predecessors. The director of national intelligence, James R. Clapper Jr., who has also been a focus of criticism for failing to police the speed at which security upgrades have been conducted throughout the intelligence community, remains in office.
Both men, and their wives, were guests at the state dinner on Tuesday night for France�s president, Fran�ois Hollande, which was widely interpreted as an indication they remained in good stead at the White House.
“The National Security Agency has told Congress that it has forced out a civilian employee after a lengthy investigation to ‘assign accountability’ for the disclosure of intelligence secrets by Edward J. Snowden, one of its former contractors,” reads the Times.
“Two others � identified only as an active-duty military member and another contractor � were ‘removed from access to N.S.A. information’ and facilities last August.”
Another contractor most probably means Mike McConnell’s cybersecurity unit at Booz Allen Hamilton, Edward Snowden’s former proxy employer at the NSA.
Business as usual at Versailles-on-Potomac.
Cynically, there is no reason to hold them in poor standing from the perspective of national leadership. They’ve done what they thought they were supposed to, which was to expand the reach and power of national cyberwar and cyber-spying.
That Edward Snowden would be perceived globally as the good guy must be vexing to them. “How can this be so?” they must wonder. “We are the good guys, not the bad guy.”
Has it not occurred to them that they’re extraordinarily lucky? There has been only one Edward Snowden. The bad guys have a pretty loyal club.
I’ll keep you informed when General Keith cashes in his chips. I would forecast a multi-million dollar signing bonus for going to head the cybersdefense operation of a major arms manufacturer plus, possibly, a million dollar book advance to tell his side of the Snowden story.
Keith Alexander — from the archives.
Permalink
02.01.14
Posted in Crazy Weapons, Culture of Lickspittle, Cyberterrorism at 1:35 pm by George Smith
Why people should pay no attention at all when someone from a famous American think tank is offering wisdom:
Instead of focusing on what we need to learn, we’ve instead fed on hype that fuels fears but doesn’t solve problems. For instance, Americans have repeatedly been told by government leaders and media pundits that cyber attacks are like weapons of mass destruction and that we are in a sort of Cold War of cyberspace …
But the fiction of a “cyber Pearl Harbor” gets far more attention than the real, and arguably far greater, impact of the massive campaign of intellectual property theft emanating from China.
“P.W. Singer is director of the Center for 21st Century Security and Intelligence at the Brookings Institution,” reads the LA Times opinion page. It mentions his book on cyberwar.
Cyber Pearl Harbor, electronic Pearl Harbor, digital Pearl Harbor. The meme is now 20 years old. P. W. Singer was 20 when it started cranking up.
I was there at the beginning, covered it for two decades. And have the archive on newspaper clippings on the matter when it was still hot and fresh nonsense.
Anyway, from the same newspaper, in 2012:
Speaking to a group of U.S. business leaders last week, Defense Secretary Leon E. Panetta issued a dire warning that foreign hackers are becoming increasingly sophisticated and that their online attacks on transportation systems, banks and other vital facilities are escalating. The worst-case scenario, he said, is a “cyber Pearl Harbor” perpetrated by state-sponsored hackers or terrorists that “would cause physical destruction and loss of life, paralyze and shock the nation and create a profound new sense of vulnerability.”
Vice magazine, doing some publicity for a paper on how the future American military might will overwhelm the usual paupers and piss ants with a sky full of 3D-printed drones:
Ben FitzGerald, [a Senior Fellow at the D.C. defense think-tank Center for a New American Security], who grew up in the Australian city of Orange, cuts an unorthodox image for a man who spends his days advising some of the highest ranking officers in the U.S. military. When he and his beard aren�t leading Pentagon war games, in which he trains officers to disable future enemy naval fleets by using hypothetical weapons such as giant microwave pulse emitters, he says he likes to visit contemporary art galleries in D.C. with his wife.
The electromagnetic pulse gun, the microwave pulse emitter. Another over 20-year old gem of which I used to like to say, the weapons that are always coming but never quite arriving. Between Wired and Aviation Week magazine, they used to be here about once a month back at the beginning.
And Ben FitzGerald looks like he was a little over ten when it all started.
His paper on 3D-printed drones, for potentially terrifying the usual list of enemies vastly poorer than the US Department of Defense, is co-authored by someone from the giant arms-manufacturer, Northrop Grumman.
This alone would be hilarious enough to reduce a rational person to tetany.
Anyway, now the microwave pulse emitters are in movies, tv and books every week, which brings us back to DD’s Law:
The probability that any predicted national security catastrophe, or doomsday scenario, will occur is inversely proportional to its appearance in entertainments, movies, television dramas and series, novels, non-fiction books, magazines and news.
Or, put another way, the probability that something bad will happen, as described or predicted by experts or any government, intelligence or quasi-corporate/government assessment agency, asymptotically approaches zero as it attains widespread use in popular entertainments. (And that�s usually very early in the development cycle.)
Therefore, you can bet your sweet bippy there�s never going to be an electronic Pearl Harbor, or an electromagnetic pulse attack, or a national blackout caused by Chinese hackers, or people dieing from a ricin mailing even though it�s so easy to make. And al Qaeda does not come back from being hided for more than a decade. No one gets a second chance.
Summed up: Too many bad movies, too much bad television, too much fear-making as edutainment, passed off as serious news, advised by bad people slumming from the national security industry, their purpose primarily maximization of employment. Everything touched by it, tainted by an intrinsic badness. And it is definitely not supported by the real world but must be maintained by a uniquely American machinery of manipulations, lies and purposeful technology-mediated confusion.
The Brookings Institution is now most famous for being the think tank that produced the scholars who made their fame on a book and public rationalizations for the Iraq War. Now notorious quacks, once passed off as the finest of intellectuals.
Publishing this kind of material is a career track. It is servanting for
the national security megaplex and arms manufacturing.
Trivia:
Australian military budget: 24 billion dollars.
US defense budget: 500 – 650 billion dollars.
The Cult of Electromagnetic Pulse — from the archives.
Permalink
01.31.14
Posted in Crazy Weapons, Culture of Lickspittle, Cyberterrorism at 12:28 pm by George Smith

A fair career summary.
Straight from the NSA:
The ongoing cyber-thefts [by China] from the networks of public and private organizations, including Fortune 500 companies, represent the greatest transfer of wealth in human history.
The 60 Minutes public relations tour:
John Miller: Could a foreign country tomorrow topple our financial system?
Gen. Keith Alexander: I believe that a foreign nation could impact and destroy major portions of our financial system, yes.
John Miller: How much of it could we stop?
Gen. Keith Alexander: Well, right now it would be difficult to stop it because our ability to see it is limited.
One they did see coming was called the BIOS Plot. It could have been catastrophic for the United States. While the NSA would not name the country behind it, cyber security experts briefed on the operation told us it was China. Debora Plunkett directs cyber defense for the NSA and for the first time, discusses the agency�s role in discovering the plot.
Spying on the paupers and piss ants:
�Well, my concern on that is specially what�s going on in the Middle East, what you see going on in Syria, what we see going on� Egypt, Libya, Iraq, it�s much more unstable, the probability that a terrorist attack will occur is going up. And this is precisely the time that we should not step back from the tools that we�ve given our analysts to detect these types of attacks.???
So here�s a partial summary of the NSA�s great achievements:
1. Infiltrating World of Warcraft because they think terrorists use it.
2. �Stopped� imaginary Chinese destroy the world by BIOS kill plot.
3. Snooping on the calls of Somali pirates and making relational plots of them.
4. Employs people who can solve Rubik�s cubes in 95 seconds.
From here:
Most of the country, at my level certainly, is still struggling with the economic deprivation and outright calamity of the Great Recession. Although corporate America has rebounded nicely, there has been no recovery for most.
And for Keith Alexander and the NSA, as well as the rest of the defense infrastructure, they saw only expansion. How unfortunate for them that Edward Snowden has spoiled it a bit.
Keith Alexander lives in the world of the plutocracy. Cash money for the day isn�t an issue. Bare bones survival isn�t on the menu. Instead, he and the structure have spent much of their time expanding operations and dreaming up threatening stories and messages to be delivered by the shoeshine men in the press, digging around in their big data suck for things which they, in encapsulated isolated delusion, believe threaten the existence of the country.

At DefCon 2012, Keith Alexander, a tech chicken-head biter just like you, delivering the call to national security corporate stooge-ism to save our futures and the American economy from Chinese cyberwar.
From the wires, reposted here:
The annual Defcon hacking convention has asked the federal government to stay away this year for the first time in its 21-year history, saying Edward Snowden�s revelations have made some in the community uncomfortable about having feds there.
�It would be best for everyone involved if the feds call a �time-out� and not attend Defcon this year,??? Defcon founder Jeff Moss said in an announcement posted Wednesday night on the convention�s website �
In defense of national security corporate stooge-ism, General Keith was there, anyway. He was heckled.
Meet the new boss, Mike Rogers, same as the old boss.
From The Predator State, by James K. Galbraith, 2008:
“[The] practice is clear: We live under government that as a matter of principle does what it wants.”
And General Keith Alexander of the National Security Agency was a soldier in the cause.
Permalink
01.25.14
Posted in Culture of Lickspittle, Cyberterrorism at 1:51 pm by George Smith
PBS rebroadcast a cyberwar bit from October recently. Google News displayed it prominently for a couple days. And that makes it worth commenting on again in its completely tone-deaf qualities, a brief piece trying to sell the ideas that hacker culture is still new, that hacker misuse of technology can be turned into offensive cyberwar for our exceptional nation, and — last — that there’s something about this corporate stooge-ism that’s cool.
Originally commented on here:
In five minutes PBS delivers every cliche written in the last quarter century about the genius and talent of young hackers and how they�ll change the world.
We must allow offensive corporate computer security so good guy young hackers can hack attack the bad guys back. This is the prescription of the a NSA man, Stewart Baker, doing public outreach for his old agency …
But back to the main thing at PBS, excerpted (it’s posted with a new air date but it’s actually a re-treaded paste-up from October):
RICK KARR: Stuart Baker is former general counsel of the NSA who�s now a computer security consultant.
STEWART BAKER: They can steal your designs. They can steal your– knowhow. They can steal your customer list and your internal analysis of what the biggest problems are in your product. This is pretty scary.
RICK KARR: The bad guys are mostly working from China and former Soviet states. They�re well-trained. Some of them are protected by — or even working for — their governments, so they don�t care about getting caught. And they might be able to do even more that steal information from businesses. Security experts worry that they could cripple the banking system … or shut down parts of the electric grid. Baker says … American businesses need a new mindset if they�re going to defend themselves.
STEWART BAKER: I’m a big believer that– the best defense is an offense. And– if we’re going to have an offense– we’ve got to have people who are really talented drawn to that field.
Definitions of role and context are important: Stewart Baker is a lawyer/mouthpiece for the NSA. And it has been part of his job to push the extremely unpopular idea that computer crime law needs to be rewritten to allow corporate America to go vigilante and strike back of those it thinks have attacked it in cyberspace.
This toxic concept is roped into a hackneyed discussion of hacker/computer security training at Carnegie-Mellon’s CyLab:
RICK KARR: People like these college undergraduates, who just might be able to save America�s corporations and governments from the bad-guy hackers: They�re students at Carnegie Mellon University, one of the nation�s top computer science schools … and they�re learning to fight off the bad guys … by thinking the same way they do. They�re learning to be the good guy hackers.
DAVID BRUMLEY: You have to understand and be able to anticipate how attackers are going to come at you. ‘Cause if you’re only doing defense, if you don’t look at offense at all, you’re always reacting and you’re always one step behind.
RICK KARR: Computer security professor David Brumley says … it�s tough stuff to teach … because the brand-new, cutting-edge cyberattack of today will be available to anyone with a web browser by next week.
DAVID BRUMLEY: For example, my courses in computer security? We don’t have textbooks. Everything’s so new. We have to go out and look at websites, we have to go look at– the latest things from conferences, and really teach from that. Every year it’s a significant update.
Karr: Carnegie Mellon�s students are so good at exploiting those vulnerabilities … that the NSA enlisted them to create a game that teaches hacking skills to high-school-aged students — and paid for the job. Cylab, the university�s cybersecurity institute, is home to the to-ranked competitive hacking team in the world: the Plaid Parliament of Pwning — �pwn??? is hacker-speak for �own???, as in the hacker takes a computer over and owns it. For third straight year, the team won top honors at international contests that pit teams of hackers against one another … and utterly demolished the competition at a prestigious contest in Las Vegas.
DAVID BRUMLEY: It’s a little bit like a little, mini-cyber-war that’s going on. And you get points by how well you find exploits in your adversaries and how well you can defend against their attacks. They’re– secure from the normal internet and they’re set up specifically for this purpose.
RICK KARR: How stiff is the competition here? I mean, who’s on your heels …
MALE STUDENT #3: Man, so, you know, who’s not? There’s all sorts of government contractors who have, you know, teams that we compete with. And, you know, they do this professionally.
RICK KARR: �Hacker??? is a label the students embrace. The word has a long history in computer science circles — where it was originally meant as praise. The students say … it still can be.
MALE STUDENT #2: We don’t think of it as bad. We think of it as– getting a deeper understanding for how something works in order to make it do something that maybe it wasn’t intended to do but it’s capable of doing.
ANDREW CONTE: It’s often the people who as young high school students they started goofin’ around with– electronics or computers, and they started figuring out, you know, how to do simple attacks, how to get inside of– machines.
RICK KARR: Andrew Conte is an investigative reporter at the Pittsburgh Tribune-Review who�s written dozens of articles about hackers and cybersecurity.
ANDREW CONTE : And at some point they make the decision. You know, “Am I going to be– a good hacker or a bad hacker? And there’s not that much difference between them in terms of– their abilities. Huge difference in terms of their motivations.
RICK KARR: That raises the question of how wise it is to teach these abilities to students barely out of their teens … with unknown motivations. Cylab graduate student Peter Chapman says not to worry.
The talk about young hackers, their aptitude for technology and natural inquisitiveness is now well over twenty years old, as old as the fact that new computer vulnerabilities are created with every update.
What’s so utterly clueless about the philosophy, and I think it’s easily identifiable by readers, is the recruitment of “hackers” into corporate stooge-ism for saving American business and military/intelligence/government interests.
Edward Snowden was just such a corporate stooge, a contract worker for Booz Allen Hamilton, at the National Security Agency. Until he took matters into his own hands.
Another open secret here is the veiled mention of the DefCon/BlackHat meetings, “a prestigious contest in Las Vegas.”
DefCON/BlackHat, particularly the latter, is a recruiting ground for the NSA and its arms manufacturer/computer security operation contractors. Another way of looking at is to call it a debutantes ball
, a Rose Queen contest, for advancement into corporate stooge work in the national security megaplex.
And we know how that’s turned out. US taxpayers have lavishly funded the biggest makers of untrustworthy networks in the world.
The paradox remains Edward Snowden. He is the only person, outside of Bradley Manning, who decided, at great personal cost, that something needed doing to change the conversation.
A well-paying job in the US economy of fear buys a lot of corporate stooge-ism and loyalty.
But it’s not going over well anymore outside the hermetically-sealed world of national security.
Hacker culture (or its way of thinking) never meant corporate stooge-ism. The NSA and mainstream media has regularly taken this old subject and tried to refashion it into the idea that using computer hackers as corporate lackeys and fulfillment servants for defense contractors is great stuff for the country.
There’s nothing special about people who solve Rubik’s Cube puzzles in 90 seconds except its use as a brag.
Well, yes, solve that Rubik for the rubes so as to distract from a larger unpleasantness: The NSA’s data suction contributed nothing on the discovery of terrorist attacks, few or many, depending on your point of view.
Note again:
RICK KARR: Cybersecurity consultant Stewart Baker says … sometimes it makes sense for a company that�s been the target of bad-guy hackers to engage in a little digital breaking and entering of its own — to hack back, in other words. He thinks it could be an important weapon in the cybersecurity arsenal. But it isn�t always so clear-cut ethically. Or legally, because in can violate federal computer security laws.
STEWART BAKER: I have been making a very public– argument that we should allow this and we should read the Computer Fraud and Abuse Act to permit it.
STEWART BAKER: I’m a big believer that– the best defense is an offense. And– if we’re going to have an offense– we’ve got to have people who are really talented drawn to that field.
RICK KARR: People like these college undergraduates, who just might be able to save America�s corporations and governments from the bad-guy hackers: They�re students at Carnegie Mellon University, one of the nation�s top computer science schools …
The story line is now the opposite and black is not white. American people, and a lot of others worldwide, need saving from our corporations, the national security business and its corporate stooge-ism disguised as the preservation of freedoms.
MORE LATER…
Permalink
01.06.14
Posted in Bombing Paupers, Culture of Lickspittle, Cyberterrorism at 1:55 pm by George Smith
The US has the biggest national security infrastructure in world history. It’s globe-spanning. And what’s its purpose? To hammer poor people, mostly.
Nothing advertised it more than, once again, 60 Minutes’ lame publicity work for the National Security Agency.
Let’s stop a moment and look again at what the NSA chose to show on television.
From the transcript at Cryptome:
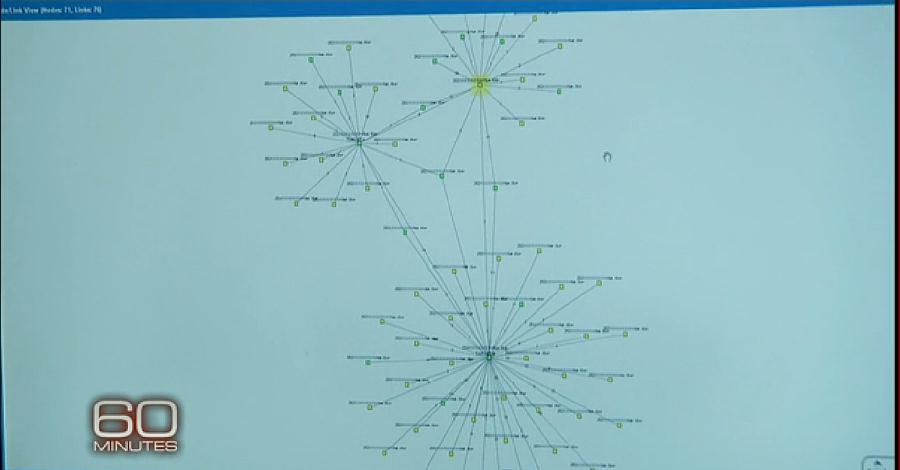
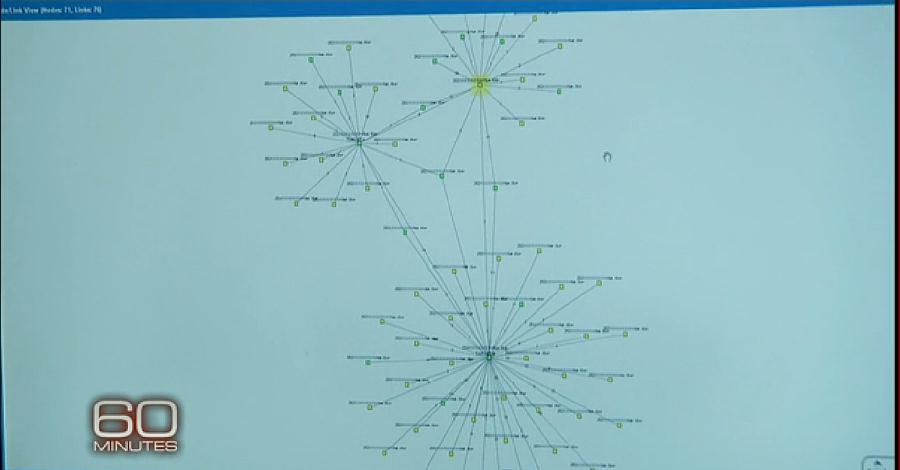
Metadata has become one of the most important tools in the NSA�s arsenal. Metadata is the digital information on the number dialed, the time and date, and the frequency of the calls. We wanted to see how metadata was used at the NSA. Analyst Stephen Benitez showed us a technique known as �call chaining??? used to develop targets for electronic surveillance in a pirate network based in Somalia.
Stephen Benitez: As you see here, I’m only allowed to chain on anything that I’ve been trained on and that I have access to. Add our known pirate. And we chain him out.
John Miller: Chain him out, for the audience, means what?
Stephen Benitez: People he’s been in contact to for those 18 days.
Stephen Benitez: One that stands out to me first would be this one here. He’s communicated with our target 12 times.
Stephen Benitez: Now we�re looking at Target B�s contacts.
John Miller: So he’s talking to three or four known pirates?
Stephen Benitez: Correct. These three here. We have direct connection to both Target A and Target B. So we’ll look at him, too, we’ll chain him out. And you see, he’s in communication with lots of known pirates. He might be the missing link that tells us everything.
The disconnect from our world and theirs is total. They’re using all their massive computing, relationship-mapping software and data sucking power to spy on people who are among the poorest and most desperate in the world. They are “chaining” them out.
Look at the photos on Cryptome.
The NSA is showing the young people bent over their computers. They think they’re defending the country against foreign threats.
What they’re really doing is spying on the pathetic in the worst places of the world using virtually unlimited technological resources. They should be ashamed of themselves. And Edward Snowden has brought them a measure of it.
Somali pirates pose no real threat to Americans. More die, per year, from attacks by angry bees.
Take a look for yourself.
Such bad guys.
Yet this is the example of metadata sifting of the networks of global enemies the NSA chose as an example to show the American people on prime time television.
The NSA workers shown are just more cogs in the big machine, a machine that bears no resemblance to a military that once existed to destroy the Axis powers.
That is all gone.
In its place, a monstrous and growing device that’s been at it for well over a decade, grinding after the paupers and the piss ants even after an original threat has been annihilated, selling it forward by convincing only the gullible that the targets pose serious threats to the country.
Under this mechanism of distortion and unreality, one can justify anything.
The people who make untrustworthy networks:
Many of the cryptologists skipped grades in school, earned masters degrees and PhDs and look more like they belong on a college campus than at the NSA.
Actually, [solving] the Rubik�s cube took [one of them] one minute and 35 seconds.
Recent score card:
Afghanistan: Hammering poor people. Majority of Americans want to leave, feel it’s not worth it, are ignored. Malnutrition worsening.
Libya: Hammered poor people to depose one famous dictator. Created failed state.
Syria: Resisted hammering poor people for the sake of getting at one famous dictator.
Iraq: Hammered poor people for a decade, rendered country into ruins, then left. Country now in bloody civil war.
What Keith Alexander, director of the NSA says:
“Well, my concern on that is specially what’s going on in the Middle East, what you see going on in Syria, what we see going on– Egypt, Libya, Iraq, it’s much more unstable, the probability that a terrorist attack will occur is going up. And this is precisely the time that we should not step back from the tools that we’ve given our analysts to detect these types of attacks.”
Permalink
12.31.13
Posted in Culture of Lickspittle, Cyberterrorism, WhiteManistan at 10:47 am by George Smith
60 Minutes, infamously:
John Miller: Could a foreign country tomorrow topple our financial system?
Gen. Keith Alexander: I believe that a foreign nation could impact and destroy major portions of our financial system, yes.
John Miller: How much of it could we stop?
Gen. Keith Alexander: Well, right now it would be difficult to stop it because our ability to see it is limited.
One they did see coming was called the BIOS Plot. It could have been catastrophic for the United States. While the NSA would not name the country behind it, cyber security experts briefed on the operation told us it was China. Debora Plunkett directs cyber defense for the NSA and for the first time, discusses the agency�s role in discovering the plot.
Debora Plunkett: One of our analysts actually saw that the nation state had the intention to develop and to deliver, to actually use this capability– to destroy computers …
So the BIOS is a basic input, output system. It’s, like, the foundational component firmware of a computer. You start your computer up. The BIOS kicks in. It activates hardware. It activates the operating system. It turns on the computer.
This is the BIOS system which starts most computers. The attack would have been disguised as a request for a software update. If the user agreed, the virus would�ve infected the computer.
John Miller: So, this basically would have gone into the system that starts up the computer, runs the systems, tells it what to do.
Debora Plunkett: That’s right.
John Miller: –and basically turned it into a cinderblock.
Debora Plunkett: A brick.
John Miller: And after that, there wouldn’t be much you could do with that computer.
Debora Plunkett: That’s right. Think about the impact of that across the entire globe. It could literally take down the U.S. economy.
John Miller: I don’t mean to be flip about this. But it has a kind of a little Dr. Evil quality– to it that, “I’m going to develop a program that can destroy every computer in the world.” It sounds almost unbelievable.
Debora Plunkett: Don’t be fooled. There are absolutely nation states who have the capability and the intentions to do just that.
John Miller: And based on what you learned here at NSA. Would it have worked?
Debora Plunkett: We believe it would have. Yes.
From Sherlock, the BBC:
Jim Moriarty, in The Reichenbach Fall: “You don�t really think a few lines of computer code are going to crash the world down around our ears, do you? I�m disappointed, I�m disappointed in you, Sherlock �
“I knew you�d fall for it. That�s your weakness. You always want things
to be clever.”
There is old precedent for this. The NSA does have an obscure record of issuing broad claims on how easy it is to crash things in the US, although most would be hard-pressed to put their finger on it.
One example from the past revolved around an NSA-conducted war game, or mock-up penetration test, dubbed Eligible Receiver in 1997. Eligible Receiver was used, by the NSA working through the press, to get out the message that foreign cyberattack could easily be catastrophic for the United States.
It’s now sixteen years beyond Eligible Receiver. No such cyberattacks occurred. However, the old footprint of Eligible Receiver was quite large in the mainstream press.
It is not unfair to look at it as a propaganda campaign, backed up by only small nuggets of truth, the purpose of which was to boost cyberdefense spending. I covered it extensively on the old home page of the Crypt Newsletter.
Here is one of the old NSA claims from Eligible Receiver:
Bob Drogin of the Los Angeles Times invoked the Pentagon ghost story of Eligible Receiver � the secret wargame conducted two years ago [in 1997] which proponents of �electronic Pearl Harbor??? insist demonstrated the nation could be flattened by cyberattack.
Drogin wrote: �The [Eligible Receiver] hackers broke into networks that direct 911 emergency systems.???
It was a clear and rather extravagant error.
Appearing in June of 1998 to testify before Congress, Ellie Padgett, deputy chief of the National Security Agency�s office of defensive information warfare spoke of how Eligible Receiver addressed the alleged vulnerability of the 911 phone system.
In a simulated exercise, Padgett said, �we scripted (an) Internet message (that) would be sent out to everybody saying there was a problem with the 911 system, understanding that human nature would result in people calling the 911 system to see if there was a problem.???
The working idea in this part of Eligible Receiver revolved around the hypothesis that many people viewing the message on the Internet in a newsgroup might panic and phone their local 911 trunk, causing a jam-up on the line.
�It can probably be done, this sort of an attack, by a handful of folks working together . . .??? Padgett said.
This is an extremely far cry from Drogin�s assertion that the 911 system was broken into by alleged Eligible Receiver hackers. In fact, it has nothing at all to do with breaking into a 911 computer system, whatever that might be.
However, it is consistent, thematically, with the flavor of the mythology propagated on Eligible Receiver �
In fact, during an interview with Crypt Newsletter in the summer of 1998 concerning Eligible Receiver, a Pentagon spokeswoman for the affair asserted �no actual switching systems??? were broken into at any time during Eligible Receiver. She went on to say that Eligible Receiver had only simulated these attacks on NSA computer networks set up to emulate potential domestic national systems.
Nevertheless, Drogin also wrote in paragraph two of the Times piece: �In less than three months, the [NSA’s Eligible Receiver hackers] secretly penetrated computers that control electrical grids in Los Angeles, Washington, and other major cities.???
In 1997, this made the grand assumption that Americans were broadly plugged into the internet, read the Usenet and that the result of a toxic post, like old computer virus hoaxes, would cause people everywhere to overwhelm their local 911 trunks.
Seriously.
Trivia note: Edward Snowden was fourteen at the time of Eligible Receiver.
More as the day continues.
Number of people on food stamps in 2013: between 47 and 48 million.

Keith Alexander, directly from the NSA’s web page, as early as 2012:
The ongoing cyber-thefts [by China] from the networks of public and private organizations, including Fortune 500 companies, represent the greatest transfer of wealth in human history.
Why harp on this?
More than anything else it shows the total disconnection between those at the very top of the national security megaplex and everyone else.
Most of the country, at my level certainly, is still struggling with the economic deprivation and outright calamity of the Great Recession. Although corporate America has rebounded nicely, there has been no recovery for most.
And for Keith Alexander and the NSA, as well as the rest of the defense infrastructure, they saw only expansion. How unfortunate for them that Edward Snowden has spoiled it a bit.
Keith Alexander lives in the world of the plutocracy. Cash money for the day isn’t an issue. Bare bones survival isn’t on the menu. Instead, he and the structure have spent much of their time expanding operations and dreaming up threatening stories and messages to be delivered by the shoeshine men in the press, digging around in their big data suck for things which they, in encapsulated isolated delusion, believe threaten the existence of the country.
When one sees and hears the cant from on high about virus threats to the US financial system and the Chinese cyberwar operation being the greatest transfer of wealth in history and you’re left asking for help at Christmas time, believe you me, it really gets under the skin.
In fact, it’s personal. And it should be so for lots of other Americans, if they ever become more familiar with the subject.
Still more to come.
Liquidate your life in the sharing economy
In which the upper crust and their immediate servants not yet rendered obsolete show how bad they are by leveraging the desperate with smartphones swipe-your-finger apps:
Kim Sundy’s husband kept heckling her nonstop to get her Christmas list to him.
“When I hired the puppet, it got him off my back,” she said.
For $15, the Ann Arbor Mich.-based blogger outsourced the problem to a puppeteer on Fiverr.com who created a short video of a puppet rapping her Christmas list …
Then there is the unselfconscious oaf of wealth, “a chief technology officer,” passed off as someone who thinks of himself as a brilliant do-er in the new world.
The assistants, according to Fancy Hands, will do “anything that doesn’t require us to physically go somewhere for you. Anything a smart, patient, Internet-savvy person with a cellphone can conquer,” as long as it is legal. Plans run from $25 a month for five requests to $65 a month for 25 requests.
For Chicago’s Harper Reed, whose storied career has included chief technology officer gigs for Barack Obama’s presidential re-election campaign and Threadless.com, using services like Fancy Hands and TaskRabbit is just plain “economic.”
“I have a very small company. I don’t have enough money to pay a personal assistant,” he said.
The tasks he hands out aren’t exactly ordinary � things like, “Where can I buy a foghorn for my father for Christmas?” along with sourcing vegan Christmas dinners …
The article gets only one person on the other side, someone newly unemployed who has turned to free-lance micro-paying gigs serviced by bike delivery.
“[Kevin Wagner, a] 34-year-old Chicagoan was laid off from his sales job in August and learned on Lifehacker.com that regular people were making extra money by performing odd jobs with TaskRabbit,” reads the Tribune.
“The Loop resident with a bike has picked up several jobs delivering items, and he has acted as a handyman, including assembling a lot of Ikea furniture … Depending on the week and how much time he has, he’ll make $20 to $400 a week at TaskRabbit.”
One suspects the latter figure is an exaggeration, like most quotes from unemployed people reduced to taking gig work in the on-line bazaar. Few want to tell you what they really earn.
For me, Mechanical Turk has been worth, on average, six dollars a week, at best, an occasional nine, never really exceeding 45 cents an hour, which allows you to determine how much time you need to put in to satisfy the whims of the corporate or academic crowd-sourcing chiseler.
In southern California, acting as a delivery man for Task Rabbit would be suicidal. There simply weren’t enough gigs in Pasadena, when I looked at Task Rabbit, to make them in any way profitable. If you bicycled them in town, perhaps almost.
But an auto is necessary for most of southern California, even much of
Pasadena, and the cost of gas puttering here and there for micro-payments being a gofer to the upper class would annihilate most earnings. This, in the same way that Mechanical Turk’s miniscule payments are significantly eaten into by the cost in electricity just to run the computer you do them on.
It is ludicrous to expect anyone to entertain the idea that people can revitalize themselves economically using the petty networking schemes developed by the tech industry under the euphemism of the sharing economy.
It’s aptly described as gig slave and servant labor in which smartphone and network tech do away with the inconvenience of having to house and pay for the food of your servant, pitting the unemployed or poverty-wage underemployed in a struggling economy against each other for the most miserly sums.
If the economic picture were healthy for the average worker, far fewer would even remotely consider taking such work. The outsource-your-vanity-work bidding services exist precisely because we live in a vulture economy.
Liquidating your life through them is no future. None are increasing the size of the economic pie, revealing only the worst (not that you needed to be told) about the people who burble about how great they are in the mainstream press.
And finally, The Disenlightenment rolls on, provenance — WhiteManistan
The stupid become more concentrated.
Permalink
12.24.13
Posted in Culture of Lickspittle, Cyberterrorism at 4:43 pm by George Smith

I�m going to repeat myself in re-use of this from a few months back because there�s really no better way to say it: The US acts as if it is the exceptional nation in cyberspace. It reserves the right to criticize and lecture others on what constitutes proper conduct but reserves the right to do what it pleases because of its alleged exceptional nature.
The US, you see, only wages cyberwar, or cyber-espionage, campaigns in defense of freedom and to keep Americans safe. No other nations do similar things. They only cyber-spy on us and probe the net infrastructure to cause damage and steal our wealth.
But this country is now in a terrible position to talk terms in cyberspace, starting with its hot clandestine war on the Iranian nuclear program and subsequent related malware spilled over into other nations and ending with the Edward Snowden revelations.
One could add a chapter or two on the growing together of the private sector and defense structure in the national security megaplex and the fact that it�s a gigantic engine, one with a major focus in finding and securing ever more revenue in tax dollars.
Mix in the apathy of a public disconnected from everything and a supine media for over ten years during the war-on-terror.
The fact that random �friends� and others are now outraged and posting on Facebook or tweeting about an agency they never thought about before is trivial, people complaining about another thing they were too busy or self-centered to pay attention to before it really got out of hand.
I would make Edward Snowden man of the year.
Whether you like what you know of him or not, he did something that made a difference. As in indirect effect of spearing the NSA, he derailed that agency’s (and the national security megaplex’s) propaganda machine on cyberwar.
Domestically, I would be surprised if anything changes.
However, when Brazil cancels an order for American-made fighter bombers for Saab Grippens and specifically says US cyberspying and a ham-handed attempt to get Snowden were the reasons one begins to see how external change might be enforced and extract a cost.
In the US, the cult of cyberwar was always one of avarice and bootlicking stenography in the mainstream and tech press.
And now, finally, at the end of 2013, no one with sense can possibly believe it’s a central issue threatening the economic lives and future of the majority, a sword of Damocles hanging by a thread which requires us to empower our computer security warriors to run over everybody, including us.
The Spiegel cover is from the beginning of November. And it is worth considering again because of the contrast it affords with an article that ran in the US at the same time, one that only demonstrated — again –how much of the mainstream American press lays down for the national security state.
The latter, almost totally removed from global sentiment on the Snowden affair, was a cover story by Kurt Eichenwald of Newsweek, absurdly entitled “How Edward Snowden Escalated Cyberwar.”
Excerpted, it’s a perfect example of a news magazine as corporate national security structure mouthpiece. its only purpose to deny reality and feebly try to beat the dead horse of threat exaggeration on cyberwar back into life:
For more than a decade, a relentless campaign by China to steal valuable, confidential information from United States corporations flourished with barely a peep from Washington. And now it might never be stopped …
The administration’s attempt to curb China’s assault on American business and government was crippled – perhaps forever, experts say – by a then-unknown National Security Agency contractor named Edward Snowden.
Snowden’s clandestine efforts to disclose thousands of classified documents about NSA surveillance emerged as the push against Chinese hacking intensified …
“Snowden couldn’t have played better into China’s strategy for protecting its cyber activities if he had been doing it on purpose,” one American intelligence official says …
“Certainly no one cares anymore about our whining about Chinese espionage. The time we had for making the case on that is long gone. Internationally, I don’t see how we recover.”
[And, finally, the ludicrous claim NSA director Keith Alexander was telling everyone before Edward Snowden’s actions put a stop to it:]
The threat of Chinese espionage is so large that Senator Sheldon Whitehouse, D-Rhode Island, who chaired the Intelligence Committee’s Cyber Task Force, proclaimed it to be part of “the biggest transfer of wealth through theft and piracy in the history of mankind.”
[Include claims, much repeated, for which there is no evidence at all]:
“Twenty years after Iraq, China has stealth fighters stolen with hacker techniques, designs for its carriers, and can pick and choose from all the research the United States has paid for,” Stewart Baker [former general council for the NSA] says. “If we find ourselves in a serious conflict with a nation with those capabilities, we could find ourselves threatening cruise missile strikes and discover that hackers shut off all the power in New York” as a warning of how much power they have to disrupt and inflict damage – potentially including the American weapons reliant on computers to operate.
As for cyberspying advancing its stealth fighter, at the time, John Pike, director of Globalsecurity.Org, dismissed it out of hand to me in e-mail. (This handy chart at GlobalSecurity shows the lag time for China’s development of advanced weapon systems against the appearance of similar US milestones. “They are twenty years behind,” said Pike.)
But readers know well that when it comes to stories on cyberwar, you can get just about any outlandish claim or exaggeration published in the American press.

Edward Snowden’s former employer, Booz Allen Hamilton, flogging the cyberwar machine in 2011.
Additional notes:
�The U.S. always reserves the right to overdo things. That�s the legacy of the last 10 years,??? [George Smith] said. �And to the world at large, it�s viewed as a nation that sees every potential problem as a nail to be hit with the hammer of the military and/or security contractors.??? — US Exceptionalism, June 2103
When you let the people in the biggest cyberwar machine in history have whatever they want the only thing left is to turn it on everyone. If the power and resources are there to do it, it is done. Because they can.
Which is what has happened … [Through] Edward Snowden�s documents and their delivery via the Washington Post and the Guardian, one sees the world Alexander has created. It�s one that cements the global perception that people in the US computer security industry (government and private sector allies) are an untrustworthy lot, predatory and needing close oversight. — GlobalSecurity.Org

And with that, I hope you are enjoying your Christmas Eve.
Permalink
12.09.13
Posted in Culture of Lickspittle, Cyberterrorism at 6:23 pm by George Smith
Why did/does this blog provide a service? Because back in 2007, I labeled claiming terrorists were using on-line games to train national security threat inflation and quack work.
But the US cyberwar machine has always overdone things. Enemies are always everywhere. And even though they’ve been wrong about everything in the last decade, nothing impedes their manias.
From the New York Times, again courtesy of Edward Snowden:
Not limiting their activities to the earthly realm, American and British spies have infiltrated the fantasy worlds of World of Warcraft and Second Life, conducting surveillance and scooping up data in the online games played by millions of people across the globe, according to newly disclosed classified documents.
Fearing that terrorist or criminal networks could use the games to communicate secretly, move money or plot attacks, the documents show, intelligence operatives have entered terrain populated by digital avatars that include elves, gnomes and supermodels.
The spies have created make-believe characters to snoop and to try to recruit informers, while also collecting data and contents of communications between players, according to the documents, disclosed by the former National Security Agency contractor Edward J. Snowden. Because militants often rely on features common to video games � fake identities, voice and text chats, a way to conduct financial transactions � American and British intelligence agencies worried that they might be operating there, according to the papers.
Online games might seem innocuous, a top-secret 2008 N.S.A. document warned, but they had the potential to be a �target-rich communication network??? allowing intelligence suspects �a way to hide in plain sight.??? Virtual games �are an opportunity!??? another 2008 N.S.A. document declared.
But for all their enthusiasm � so many C.I.A., F.B.I. and Pentagon spies were hunting around in Second Life, the document noted, that a �deconfliction??? group was needed to avoid collisions � the intelligence agencies may have inflated the threat.
May have inflated the threat. Get rewrite and go for historical accuracy. They always inflated the threat.
Why where so many “hunting around” in Second Life?
Cue Internet and dog joke, paraphrased: “In cyberspace nobody knows you’re just another asshole from the US national security megaplex.”
Anyway, from 2007 — why, here, of course:
“One radical group, called Second Life Liberation Army, has been responsible for some computer-coded atomic bombings of virtual world stores [in the on-line fantasy game called Second Life] in the past six months,” wrote a reporter for the Australian, today.
“On screen these blasts look like an explosion of hazy white balls as buildings explode, landscapes are razed and residents are wounded or killed.
“With the game taking such a sinister turn, terrorism experts are warning that [Second Life] attacks have ramifications for the real world. Just as September 11 terrorists practised flying planes on simulators in preparation for their deadly assault on US buildings, law enforcement agencies believe some of those behind the Second Life attacks are home-grown Australian jihadists who are rehearsing for strikes against real targets…”
Entitled “Virtual Terrorists,” alert reader Cubic Archon tipped your friendly neighborhood GlobalSecurity.Org Senior Fellow to this bit of titillating terror infotainment dressed up as real news.
Of course, it is not good scary terror infotainment unless experts are on hand to inform you that it has been a subject of quiet concern for some time. But now the danger has become too great, the threat impending, and they must speak!
“Terrorist organisations al-Qa’ida and Jemaah Islamiah traditionally sent potential jihadists to train in military camps in Pakistan, Afghanistan and Southeast Asia,” continues the Australian. “But due to increased surveillance and intelligence-gathering, they are swapping some military training to online camps to evade detection and avoid prosecution.”
“Rohan Gunaratna, author of Inside al-Qa’ida, says it is a new phenomena that, until now, has not been openly discussed outside the intelligence community.
“But he says security agencies are extremely concerned about what home-grown terrorists are up to in cyberspace. He believes the dismantling and disruption of military training camps in Afghanistan and Pakistan after September 11 forced terrorists to turn to the virtual world.”
” ‘They are rehearsing their operations in Second Life because they don’t have the opportunity to rehearse in the real world.'”
“Intelligence and law enforcement agencies in the US and Australia are so concerned they have established their own reality world games in a bid to gain the same experiences as the virtual terrorists.
“Monash University academic and former Office of National Assessments intelligence officer David Wright-Neville agrees that online games and virtual worlds are being used by potential terrorists to hone their knowledge base … Intelligence analyst Roderick Jones, who is investigating the potential use of the games by terrorists, says [Second Life] could easily become a terror classroom.”
Are you ready to your local anti-terror forces stamp out the on-line game? Or are your eyes rolling over yet another ad hoc squad of experts ready to say anything to a news organization in the process of concocting another exciting fraud from the terror wars?
“Basically, we have a succession of inaccuracies about Second Life in the first place (e.g. you can’t leave ‘a trail of dead and injured’ there, even virtually, given that there’s no permanent death or injury built in; the ‘Second Life Liberation Army’ was a media publicity stunt,” writes Cubic Archon in e-mail.
He added that the news piece offers “ridiculous sourceless commentary.”
Archon finds the next claim laughable.
“Kevin Zuccato, head of the Australian High Tech Crime Centre in Canberra, says terrorists can gain training in games such as World of Warcraft in a simulated environment, using weapons that are identical to real-world armaments.”
“World of Warcraft is a fantasy game,” the e-mailer points out. “So, in the real world, terrorists are going to be attacking with magic swords and fireball spells?”
Since Archon makes good points about the meretriciousness of claims that terrorists can use Second Life as a way to plan attacks, DD turns the real estate over to him:
“I am a fairly long-term user of Second Life and, while it has some great potential for certain types of teaching and real-world modeling – it’s used increasingly by architects, for instance – this is about as credible a threat as the one about school shooters building models of their school in Counterstrike and using them to rehearse attacks. Bouncing about in an online simulation isn’t combat training.
“And the idea that it is being used by al Qaeda to recruit, any more than, say, Myspace, is sourceless nonsense. There are all sorts of ‘comedy’ names and groups in Second Life, and it would surprise me immensely if people hadn’t started up al Qaeda type groups, perhaps with virtual explosive belts, to satirise the media obsession with them. To be honest, this sort of article almost makes me want to do that myself – or maybe build a replica of Pearl Harbour and start bombing it from virtual aeroplanes.
“You know, it would be terrific if Second Life was really as good and realistic as it is portrayed here, that you could actually learn how to do something as complex as build explosives or field-strip a rifle from the comfort of your own bedroom, but unfortunately it isn’t.”
Supplying related URL’s, Archon writes: “Another past example came from Threatswatch.org here. [This] was quite roundly panned by Second Life users in comments and on various blogs.”
Continues the Australian: “US terrorism expert Bruce Hoffman, from think tank RAND Corporation, says … ‘We have to contest this virtual battle space in much the same manner as we are very successfully doing in other traditional forms.'”
The item on terrorists and Second Life, from Threatswatch, back in 2007:
A Daily Brief item today pointed out some disturbing developments in the virtual world of Second Life. While at first glance one might be dismissive of developments in the �fake??? world, a closer look indicates that Second Life has the potential to enhance the terrorist threat.
The FBI and others recently began pointing out their shift in thinking that terrorist threats to the homeland will come from al-Qaeda sleeper cells such as the 9/11 hijackers and instead will come from self-radicalized individuals and groups. The so-called �Ft. Dix Six??? are such a group, having allegedly used (at least in part) various terrorist resources online for motivation and training. Anti-terror raids in the UK and elsewhere note that those arrested are often in possession of computers that contain radical Islamic literature as well as information on how to perform pre-operational planning, use small arms, and conduct small unit tactics.
There are those who dismiss self-radicalized, self-trained groups as amateurs who are unlikely to ever conduct a successful terrorist operation, though events of so-called �sudden Jihad syndrome??? over the past five years suggest that even self-taught sad-sacks can kill or maim. Still, there is a big difference between someone who has actually trained to fight an armed conflict or conduct intelligence operations and someone who has merely read about how it is done.
Second Life bridges that gap.
In Second Life you can practice intelligence tradecraft; you can test your elicitation skills, pass off (hopefully unnoticed) notes and packages, and meet in private with co-conspirators. You can sit down in a classroom and learn how to field-strip a rifle or pistol, conduct fire-and-maneuver drills, or run through an urban combat scenario. You can send and receive money to help fund your operation and you can conduct �legitimate??? business that ends up funding terrorism. Static online training materials or even interactive-but-text-based Jihadist discussion forums cannot match the rich and substantial � if one may be excused for adopting a marketer�s language � content.
Second Life has the potential to elevate the professionalism of terrorism training. It is not real-life, but it isn�t reading comic books either.
Bottom line: You could have predicted US cyberwarriors and terrorist hunters were going to charge into on-line gaming undercover. Seeing threats everywhere, even when virtually none exist, has always been their business.
What many people didn’t realize, or refused to recognize at the time, was that the national threat assessment apparatus, from the private sector to the intelligence agencies, feeds on itself.
It recites its little stories and has always actively worked to put them into the news. And when their rumors, half-baked suppositions and crazed paranoid mutterings are published and made respectable they become a citation in someone’s pitch to start terrorist-hunting operations, in this case in on-line gaming.
From 2007 to Edward Snowden’s papers in 2013.
Permalink
11.08.13
Posted in Culture of Lickspittle, Cyberterrorism at 4:13 pm by George Smith
NSA Spy Kit — by Fiore.
Getting his ticket punched at an arms manufacturer in 2014 won’t come too soon. Do watch it.
When you’re a regular caricature in editorial cartoons and animation, there’s no room for delusion about legacy and how the agency’s work is broadly misunderstood.
Permalink
« Previous Page — « Previous entries « Previous Page · Next Page » Next entries » — Next Page »